DIY Solution
No-Code / Low-Code Software Solution Accelerates Projects & Improves ROI
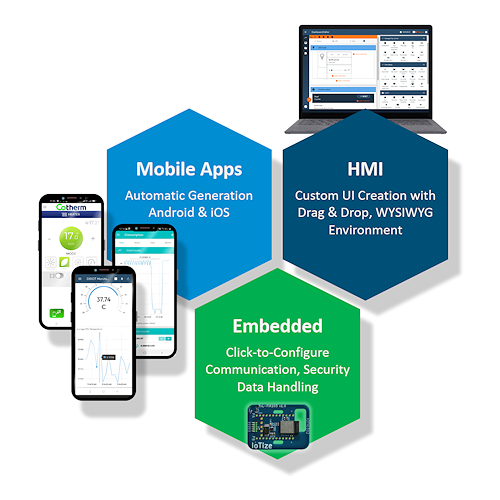
Today, customers expect mobile and cloud connectivity in products. However, the complexity of creating these connected products stops many companies from capitalizing on opportunities. Our no-code / low-code software solution transforms complex projects into simple tasks that deliver immediate results, so that your company can capitalize on IoT opportunities today!
No matter whether you're connecting to a cloud or to mobile devices, our embedded software pre-implements all the features you need. It provides communication, security, and data handling protocols that require no coding to implement. Where customization is required, it provides a Java Virtual Machine that runs your code. Product designers simply select and setup features, then add java routines for their customizations in our free IoTize Studio configuration environment.
Designers can then create user interfaces and transform these into smartphone apps in App Creator. In the drag-and-drop, WYSIWYG design environment, they can make UI with elaborate, responsive displays and controls in just minutes. These run equally as mobile apps, or as cloud dashboards.
After testing the interface, designers generate their apps in just a few clicks using our automatic app generator. They can either directly build the resulting project into a signed app, or modify the project code to further refine their UI before publishing.
Free IoTize Studio transforms wireless integration into a simple process of connection and configuration.
With App Creator, make UI with full control of graphics, layout and data flow... but without writing a single line of code.
Our automatic App Generator instantly outputs your UI as Android, iOS and Web apps, without writing a single line of code.
Add NFC, Wi-Fi, Bluetooth, LoRa, LTE-M, NB-IOT to any electronics in minutes, without writing a single line of code.
Improve the ease and security of connecting to mobiles with 3-Stroke Configuration, and Tap-to-Pair for Bluetooth and Wi-Fi.
Pre-implemented features for access control, authentication, and dynamic-layered encryption.




